With the invasion of the coronavirus pandemic, the world has changed. Businesses across the globe while practicing social distancing are dependent on the internet more than ever before. Almost all trade shows, conferences, and offline marketing initiatives are canceled. This has dramatically increased the demand for digital marketing. While it is important to stay at home and stay safe to fight the COVID virus, it is also equally important to keep businesses running and help the economy grow during these dire times. Digital usage will be the deciding factor for business continuity and profitability. While companies use new digital strategies, it is important that they adhere to the general data protection laws that have been put in place.
Governments across different countries are coming up with different data protection regulations and guidelines to safeguard user data. Thus it becomes increasingly important for digital marketers to follow these regulations or face huge penalties. All of the current reforms like GDPR and CCPA aim at helping the customers gain better control over their data by offering more transparency through data collection and usage processes. This doesn’t put an end to how digital marketers can market their products. They just have to modify their ways of collecting and using the data of consumers.
Here are some tips that a digital marketing agency or any firm involved in digital marketing can use to adhere to data protection laws prevailing across the globe.
1. Standardize the Policy for All Regions
It is advisable to maintain a standard all-encompassing policy across all target market regions. Slowly and steadily, all countries are aiming for the protection of their consumer data. These privacy laws which are applicable in one region will soon be implemented in other regions. Most countries follow their predecessors, creating policies that are quite similar to the ones already in place. This means that you don’t have to worry about your campaigns when a new policy takes effect in a different region, because ultimately most of the privacy and cybersecurity laws are more or less similar and you have already accommodated those in your standardized approach.
2. Risk Management
Organizations should create new risk management policies that are to be strictly followed by each division of the company. Here are some of the steps that should be included:
3. Website Audit
Your business is still liable and can face heavy penalties for the collection and improper use of data by third-party platforms. It’s essential for your business to audit its website in order to understand the platforms loading across different pages of your site. This may include tags and pixels that you may not be implementing directly but are piggybacked on your platforms. You need to put checks and balances in place to identify others collecting data from your website.
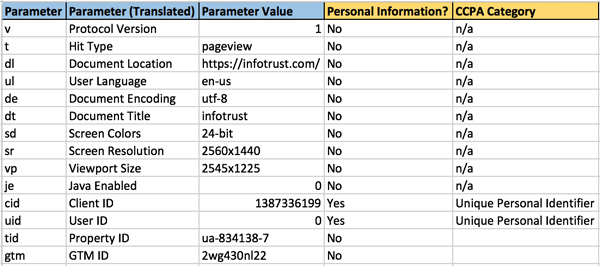
This data can be obtained using a tag audit and tag inspector. Follow these steps:
1) Identify the platforms loading on your website.
2) Understand the data collected by them by looking at the network requests they are sending from your business site to the respective server of each platform. The type of data collected by these third-party platforms should be identified. This can be done by looking at the network requests they are sending from your website to their own respective servers.
3) By using Tag Inspector, you can collect these at scale across all pages of your site and get simpler outputs to aggregate and understand the same data.
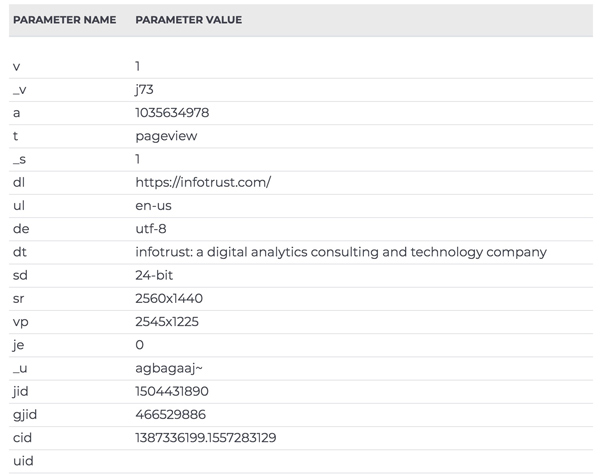
4) After identifying the data points of each platform, analyze if any data is considered personal information. Mapping of data can be done in this format for ease of understanding.
In case personal information is collected/shared/sold, you need to include this in your privacy notice and disclosures to consumers.
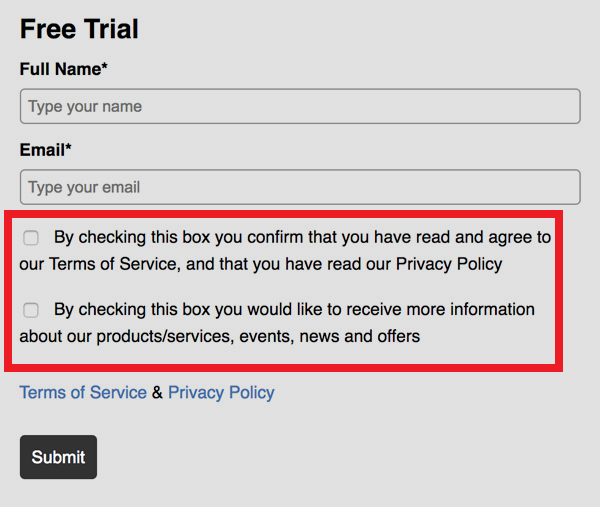
4. Obtaining User Consent
Terms and consent on your emails, campaigns and websites should be clear and not stuffed with complex language that can confuse users. The user consent should be obtained to collect information as well as to send future information.
5. Ownership in Case of Data Breach
Data breaches are not a matter of “if they happen” but rather “when they happen”. In spite of having a very secure system, always be prepared for the worst. In case of a data breach, Marketing and IT will work together as the first line of defense in complying with legal notification requirements. The appropriate point of contact should be in place in case an unthinkable data breach situation arises.
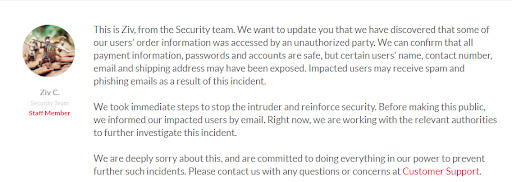
6. Immediate Breach Notification
If a security breach occurs, you should report the data breach to both your customers and data controllers. Failure to report would lead to fines and strict action against the company by data protection authorities.
Every individual in the company is entitled to report a data security breach as soon as they discover it. Recently, Oneplus informed its customers that an unauthorized party was able to access order information from the online store of Oneplus. They also pointed out what information was accessed. Here is the screenshot for the actual notice by Oneplus.
7. Providing Data Access Rights to Users
Under certain legal basis, users have the privilege to access their data that has been collected. The company should be able to provide the user with a free detailed electronic copy of the data that was collected about them. It would be good practice to share a report that includes various ways in which the user data is intended to be used.
8. Right to Be Forgotten
Customers have the right to ask for data deletion. They can make a request verbally or in writing. Additionally, companies can erase customer data after it has been used for the purpose per their consent. Every company has the right to refuse data deletion if collected for the following purposes:
9. Data Portability
Data portability laws give the users rights to their own data. This information should be in a usable format that allows easy transmission without hindrance. Companies like Google and Facebook now allow users to download their own data, generally in a machine-readable format that can be used to transmit their data to another service.
Conclusion
It’s essential that you only collect relevant data. Collecting unnecessary data just because you think that it would be useful in the future can make your present data processing and management difficult. Ultimately you need to really think whether you require the data you are collecting or not, because the older way of collecting as much data as possible will make things more difficult for you. Data minimization and relevancy should be the goal while storing the data While it may seem that CCPA and GDPR principles will terminate digital marketing, that is far from the truth. These eprivacy directives will, in fact, help companies come out ahead, especially those companies that embrace it. They will help build a good relationship with customers by fostering trust and being open about what data is being collected from customers and why. Giving consumers a choice will help create a mutual benefit — and exchange of data for more personalized and relevant experience.
This is a smart marketing strategy in the long run. It will help in business continuity in the current COVID-19 times when traditional marketing strategies cannot be implemented due to social distancing and restrictions to fight the global pandemic. As businesses embark on their new digital journey, it is important to adhere to data protection laws. This will benefit both your business and your customers. Stay safe, and keep others safe.